Organization Size-Based Technology Solutions
There are a lot of shitty people out there who will want to claim this as their own original work and the thought of that doesn't sit well with us. Therefore, CMMC-COA uses the Creative Commons Attribution-NoDerivatives 4.0 licensing model so that we retain this awesome Intellectual Property (IP), but you still get to use it. Under Creative Commons licensing, you are free to share this information, including copying and redistributing the material in any medium or format for any purpose, even commercially.
Per Creative Commons, the licensor cannot revoke these freedoms as long as you follow these license terms:
Just to reiterate, there is no endorsement of any kind for products or services listed on this website - It is entirely your responsibility to conduct appropriate due diligence and due care in selecting and engaging a product or service for implementation against CMMC practices and processes within your organization. Your responsibility, not ours! Yours!
As for what you get access to, we thought about doing something fancy with this website but we had better things to do with our time. What you can do is download latest version of the Microsoft Excel file from our shared Box drive (click on the pretty picture below) and you will have access to some pretty cool shit that includes:
- CMMC COA Awesomeness Spreadsheet for NIST 800-171 R2 & CMMC 2.0
- CMMC COA Awesomeness Spreadsheet for NIST 800-171 R3
- NIST 800-171 R3 Kill Chain
- CMMC Kill Chain (NIST 800-171 R2 & CMMC 2.0)
- Compliance Decision Making Process (CDMP)
- CMMC Assessment Preparation Guide
- Numerous useful reference documents
The NEW & IMPROVED Awesomeness Spreadsheet for NIST 800-171 has some cool features:
- Control to Assessment Objective (AO) visibility
- Crosswalk mapping to the SCF, NIST 800-53, NIST CSF 2.0, ISO 27002, etc.
- RASCI matrix (shared responsibility matrix)
- Roles & responsibilities (based on NIST NICE Cybersecurity Workforce Framework)
- Cadence for control execution (e.g., daily, weekly, monthly, etc.)
- Evidence Request List (ERL) identifies reasonable evidence for each AO
That's pretty much it - just a shit ton of very useful information for you to get compliant, so please do not bitch and complain that no one is providing any guidance on how to actually comply with CMMC practices and processes. If you do not know what to do with that information, reach out to a competent IT/cybersecurity consultant who can help you with your specific needs.
As for updates, we will update this list every so often... when we have nothing better to do in our day jobs, when we run across new tools that might be of interest or some other reason that would make us want to update the spreadsheets. It is in our interest to keep the spreadsheet updated, since we use these recommendations on a daily basis, so you have access to the awesomeness that we leverage for our own consulting needs. You're welcome, America!
CMMC Assessment Preparation Guide
Looking for some sage advice on preparing for your CMMC assessment? Your goal is to pass a CMMC assessment and it is imperative that you do not make unforced errors. In audits/assessments, unforced errors are primarily due to the assess lacking the ability to answer questions in a concise and straightforward manner. The good news for you is we made something awesome to help you prepare for your time with a C3PAO or with DIBCAC! Woohoo!
Other Very Useful CMMC & NIST SP 800-171 Resources
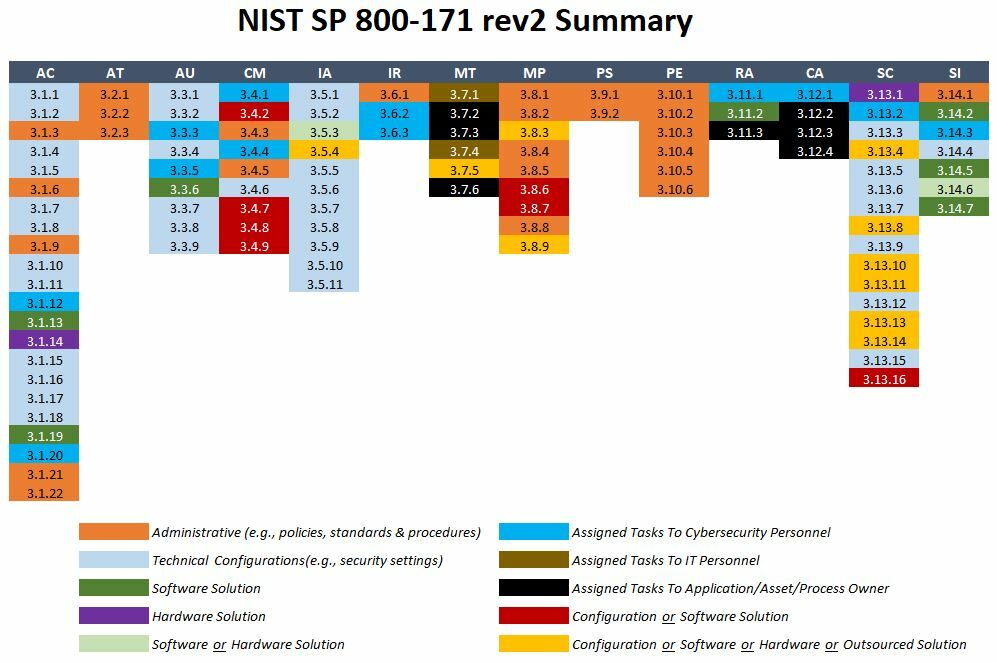
NIST SP 800-171 and CMMC are more focused on good IT practices more than hardcore cybersecurity practices. This is quite evident when you breakdown the various processes and practices to People, Processes, Technology, Data & Facilities (PPTDF) :
-
Tasks Assigned To Application/Asset/Process Owner
-
Tasks Assigned To Cybersecurity Personnel
-
Tasks Assigned To IT Personnel
-
Configuration or Software or Hardware or Outsourced Solution
-
Configuration or Software Solution
-
Hardware Solution
-
Software or Hardware Solution
-
Software Solution
-
Technical Configurations (e.g., security settings)
If you are still thirsting for knowledge, the following CMMC & NIST SP 800-171 resources are worth exploring:
-
NIST 800-171 & CMMC Maturity Spider Charts. This is a free spreadsheet to generate cool-looking spider charts for control-level maturity comparisons between current and targeted states.
-
CUI / FCI Scoping Guide. UPDATE - this new version incorporates the DoD's L2 scoping guidance. If you want to see examples of how to scope your environment using leading practices, you can download the Unified Scoping Guide (USG) as a way to scope CUI, CTI and other forms of sensitive/regulated data that your organization may store, process and/or transmit. NIST released an updated version of NIST SP 800-171 R2 (18 Jan 21) that changes wording around the scoping of the CUI environment. Specifically, "The requirements apply to components of nonfederal systems that process, store, or transmit CUI, or that provide security protection for such components." Where it is footnoted to include "system components include, for example: mainframes, workstations, servers; input and output devices; network components; operating systems; virtual machines; and applications." This replaces their older CUI Scoping Guide. The DoD has since released its own scoping guide here.
-
Non-Federal Organization (NFO) Controls. If you want to learn more about NFO controls and how that impacts both NIST 800-171 and CMMC, you can read about them here. If you are still not convinced about the need for NFO controls, the Michael Oxmal School For Consultants Who Don't Read Good is a great place to start to understand what the baseline requirements are.
-
Metaframework. For those juggling multiple statutory, regulatory and contractual obligations, you can download the Secure Controls Framework (SCF) at https://securecontrolsframework.com. The SCF is a metaframework that includes mappings for CMMC, NIST 800-53, NIST 800-171 R2, NIST 800-171 R3, NIST 800-171A R3, NIST CSF, ISO 27002 and about 100 other laws, regulations and frameworks.
-
Non-Applicable or "Self-Deleting" DFARS/FAR Clauses. For those organization that are legitimately out-of-scope for DFARS/FAR/CMMC, but are receiving contracts that stipulate compliance obligations, this Memorandum For Record (MFR) template may be useful to "prove a negative" by documenting the non-applicable nature of the contract clause. You can download that here. Ideally, the prime/sub contract would have a contract addendum to reflect this non-applicability. This is where legal counsel is recommended for any contract-specific issues.
-
CUI Training Resources. If you are looking for training resources for CUI, there are a few:
-
CMMC Self-Assessment Tool. Are you tall enough to ride CMMC? Prove it! You can use this shiny new CMMC Assessment Tool that is NIST 800-171A & NIST 800-53A based to evaluate CMMC v2.0 practices and processes (included in the CMMC-COA Awesomeness spreadsheet download). Where NIST 800-171A assessment criteria exists, it is used. Where CMMC created their own controls, NIST 800-53A assessment criteria was used. If you don't like that, we really don't care and you can create your own tool. However, NARA's CUI Notice 2020-04 stated that NIST 800-171A is the authoritative source for CUI assessment criteria, so it if is good enough for them, then it works for us.
-
International Traffic in Arms Regulations (ITAR) Reference. Not all ITAR is CUI. Not all CUI is ITAR. There is CUI that is ITAR. This guide is just a helpful reference to understand what ITAR is about and what that may mean for how you architect your network to take into account possible limitations for "foreign persons" that would be prohibited by ITAR.
-
CMMC Reciprocity & Inheritance. This article addresses the concept of reciprocity (e.g., FedRAMP) and inheritance.
-
CMMC Story Time. Trying to explain CMMC can be difficult, so we wrote a children's-style flip book to explain it! Enjoy!
- Goldilocks & The Three C3PAOs. This is a riveting tale of Goldilocks and her adventure to find the right C3PAO! Woohoo! (no C3PAOs were harmed in the making of this story).
-
CMMC Life. Coming soon! All the CMMC questions you dared not ask your RPO and much, much more! (just kidding - we know you want it, but no. hell no)